Mobile Devices Settings
- See the Mobile App Deployment guide for more insight.
Platforms Supported
Check which mobile operating systems (iOS or Android) will be available to users.
Mobile Device Saving Mode
Set how the user's credentials will be stored on the mobile device.
This only applies to the native Pyramid application used on a mobile device.
- Save User Name and Password: both credentials are stored on the device once the user sets them. When the user starts the Pyramid mobile app, they will NOT be prompted to login (similar to mobile email, security is derived from the security of the mobile device itself). The user can manually logout of the app to remove these settings.
- Save only User Name: only the user name is stored on the device. When the user starts the Pyramid mobile app, they will be prompted to supply a password to login. The user can manually logout of the app to remove the user name setting.
- Don't Save: neither credential is stored on the device. When the user starts the Pyramid mobile app, they will be prompted to supply a both set of credentials to login.
Facial Recognition
This feature is currently only supported on iPhones.
Facial recognition gives you the option to log into the mobile app without having to input a password. An Admin must first configure this for the network. In the Admin Console, select Mobile > Device Settings, and under Mobile Device Saving Mode, ensure that iOS Face ID is selected:
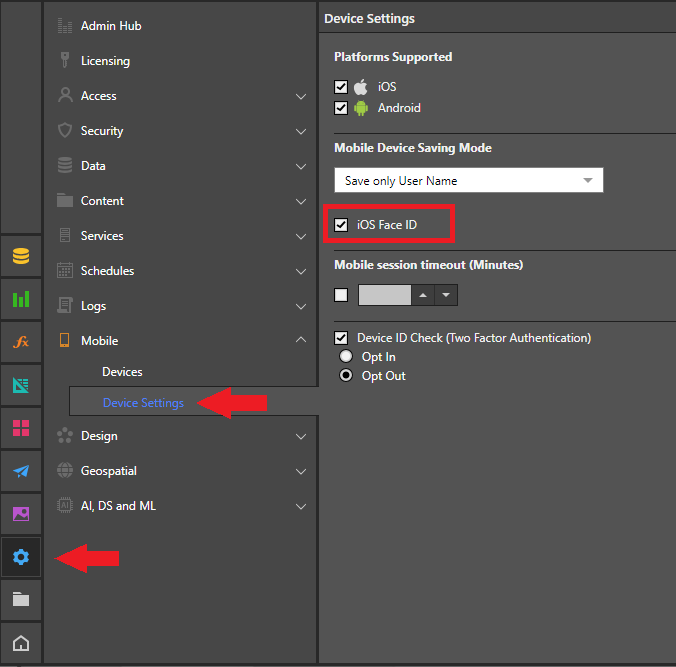
Note: You can also access this page from a quick link on Security > Server-Side Security Important: Always remember to apply any changes using the Apply button at the top-right of the workspace.
Once FaceID is configured, when you log into the app on your iPhone for the first time, you are prompted to enable it. After that, you can choose whether to enable, or disable, FaceID. For more information, see Mobile Client.
Mobile session timeout
Enable this feature to put a timeout on any mobile session. When enabled, the mobile client will auto-logout from the application after the specified time has elapsed since its last use.
Device ID Check
Enable this feature to check both a user's credentials and the ID of the connecting mobile device. If disabled, all devices can connect without limitation.
The mobile device ID check can be used to enable or block specific devices (regardless of user). New devices connecting to the system can be attached using 2 models:
- Opt In: all new devices are EXCLUDED and BLOCKED on the system by default, until an admin has enabled the device on the framework. Separate messaging options are available to inform admins when a new incoming device wants to connect to the system. Messaging must be enabled for this to operate.
- Opt Out: all new devices are INCLUDED and ENABLED on the system by default, until an admin has disables the device on the framework
Admins can see and manage devices connecting to the system on the devices page.
Device ID Check: Two-Factor Authentication
By employing the device ID check, the system facilitates two-factor authentication because 2 independent sets of credentialing data are required to gain access to the platform: the user's username and password, and , the device's machine ID. This provides a highly efficient, out-of-the-box solution for mobile authentication without 3rd party tools and related complexities.
The same mechanism also provides an elegant way to block lost devices from connecting to the system (instead of users).